)
Savvy buyers on e-commerce stores know that they should not assume that a listed item fits its description. And if the item is being sold by a third party, they know to look through the seller’s rating and feedback to check for anything suspicious before they buy.
With e-commerce being multi trillion-dollar industry, it is no surprise that it has become a primary target for unscrupulous actors. Some actors set up shops, post goods for sale, then receive the payments without delivering the item (as described or at all).
Even if the e-commerce vendor can recover the payment from the fraudulent seller and compensate the buyer, problematic transactions trigger the resource-intensive dispute resolution process, and they degrade the overall consumer confidence in the store.
Other malicious actors engage in return fraud, in which a buyer requests a refund but sends an empty package back to the retailer, keeping the purchased item. Some actors simply claim that the item was not delivered.
E-commerce providers are undoubtedly aware of these fraudulent practices and attempt to automatically block them without affecting authentic transactions.
Prevention mechanisms include giving accounts a score. New accounts or accounts with histories of many returns or abnormalities, for example, will be treated with greater scrutiny than those from accounts with a long track record and solid reputations. And, when it becomes clear that fraud took place, the offending account is swiftly shut down.
These automated algorithms have made aged, experienced accounts far more valuable to scammers. If an attacker possesses an account with a long, stellar reputation, then they have greater chances to evade the detection mechanisms.
One way for actors to procure experienced accounts is through taking them over by attacks such as credential stuffing. We found that e-commerce sites such as Amazon, eBay, and Walmart are among the most-mentioned organizations in the context of credential stuffing tools.
Another is simply to purchase them; on the underground, there is a flourishing market for aged and experienced accounts. The scheme is straightforward. One actor opens accounts and cultivates them over time with legitimate transactions. Once the account is properly mature, they sell it on the deep and dark web to actors eager to abuse them for malicious purposes.
On the underground, we can find transactions of accounts belonging to just about all e-commerce sites. However, with Amazon Prime underway, we decided to focus on accounts belonging to the retail behemoth. A close examination of these posts reveals more about the market for these accounts:
Account Types
This actor makes it quite clear why he wants to buy an aged account “with previous orders”: he wants to commit refund fraud.

An actor seeking to buy an aged Amazon account with previous orders, for refund fraud
Amazon accounts for all geographies are available. This actor is selling Amazon US accounts:

An actor selling Amazon US accounts
This actor lists accounts—at £175 each—for Amazon US, Canada, UK, Spain, Germany, and France.

An actor selling Amazon US, Canada, UK, Spain, Germany, and France accounts for £175
Account Age
How aged is an account until its ripe for fraud? The first poster is looking for something older than six months. The second post lists accounts aged 5+ years. And the final post lists accounts that are 2-10 years old.
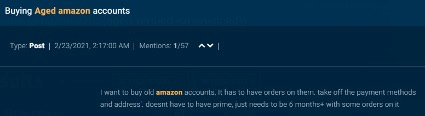
An actor seeking to buy Amazon accounts aged 6+ months, with an order history

An actor selling Amazon accounts aged 5+ years

An actor selling Amazon accounts aged 2-10 years for $1-$15
Account Prices
Overall, the prices per accounts vary. Some posts offer them for as low as $1 each, while others cost in the hundreds. These relatively low prices could indicate that account sellers can generate them in bulk. Otherwise, it would not make sense for them to invest so much manual effort in opening and cultivating them while selling for such small profits.
Advanced Evasion
Finally, we find some indication that buyers are doing more than simply purchasing the username and password. This actor writes that he wants to buy an aged Amazon account, not only with previous orders, but with browser cookies and SOCKS proxies. This indicates that the actor wants to be able to emulate the original system and location of the account creator, an added layer of evading detection.

An actor seeking to buy aged Amazon accounts including browser cookies and SOCKS proxy information
What should be done?
The advice to consumers is simple: just because a seller has a great reputation, it doesn’t mean that they are legitimate. Before you buy, if you notice anything suspicious on the account—the seller is selling items that are very different, much greater quantities, or more expensive than what was sold in the past— pass on the offer.
Maybe be a good citizen and report it, too. Account providers, meanwhile, ought to limit bulk-creation of accounts and monitor existing accounts to find any indications that they were exchanged. They also should monitor underground forums to understand the market for these accounts—who is selling them, how many, and for how much?
The game between security practitioners and cybercriminals is a constant cycle of catand-mouse. As vendors implement new protective measures, attackers seek weak links in the chain and innovate new tactics, techniques, and procedures to exploit them. Hopefully, defenders will be just as agile in identifying and countering every emerging threat.
)
)
)
)