)
The Log4j vulnerability is the topic on everyone’s lips, and Github is no exception. At 223 repos and counting, threat actors don’t need to look far to find the exploits they need.
CVE-2021-44228, also known as Log4Shell, is a remote code execution vulnerability in the Apache Log4j library. While this vulnerability is just over a week old, indications suggest that it poses a severe risk due to its ease of exploit as well as the widespread use of the compromised code library on internet-connected servers.
Github, the Microsoft-owned open-source community of over 73 million developers, is an excellent place to follow developments surrounding CVEs. On Github, contributors share both defensive and offensive tools as well as information and insights surrounding emerging vulnerabilities.
A review of activity surrounding this CVE on Github confirms that this is indeed an unprecedented event. Through December 18, seven days after receiving an official CVE designation, Log4j has been mentioned in 223 unique repositories - vastly eclipsing every other vulnerability from 2021. To provide some relative context, the runner-up, CVE-2021-41773 (a path-traversal vulnerability in Apache HTTP server, designated on 9/29), has only been mentioned in 164 repos.

This is particularly remarkable considering that the Log4j flaw is just over a week old, while the other CVEs have been around since some point in 2021, whether several weeks or even months.
This represents an exceptional first week. If we compare Log4j’s first week to the first weeks of the next four CVEs as listed in the figure above, Log4j generated 16% more relevant repos than the next four leading CVEs combined!

Clearly, Log4j is attracting an unprecedented degree of attention from the Github community. This could be a result of the attention that it is receiving from the broader cybersecurity world, as well as because of the relative simplicity of exploitation, which allows many actors to create tools and exploits of their own.
What's in the code?
These 223 Github repositories vary in nature. Some are defensive by design, including lists of IOCs and various threat hunting tools. Others, however, are ostensibly offensive tools, such as demos and exploits for cyberattack.
Defensive Repos:
Defensive repos relating to Log4j include tools, data, and analyses intended to assist defenders in protecting their environments from potential Log4j exploits. These include lists of IOCs, information about affected Java applications, locally run scanners, and forensic analyses of attacks.
For example, the repo depicted in the screenshot below includes a list of IOCs relating to Log4j. These include malicious domains and IP addresses, as well as hashes of binaries and payloads and YARA rules. Defenders can integrate IOCs into their SIEMs, SOARs, and endpoints in order to block malicious exploits of the vulnerability.

This second repo as pictured in the below screenshot presents hashes of vulnerable versions of Log4j. It can be used to identify any vulnerable assets within a particular environment:

Third, this Github member shared a server they had created that can be used to check any Java program to determine if it is susceptible to the vulnerability:

This fourth repo includes a scanner that enables network administrators to check if they are hosting vulnerable applications:

Further, this fifth tool claims to patch the vulnerability at runtime of any Java software. Presumably, it can be used when updating/patching is not a viable option.

Lastly, in this repository, another Github member analyzes a Log4j attack, tracing it back to an attacker from an IP address in St. Petersburg attempting to install a cryptominer.

Offensive Repos:
Offensive repos include tools that assist in the exploitation of the Log4j vulnerability. In the hands of authorized security practitioners, these tools can be used to test if an environment is properly protected. However, they are just as easily accessed by threat actors, who can then abuse the tools for malicious ends.
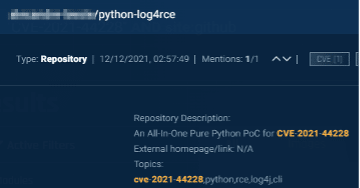
The following posts include demos and proof-of-concept exploits, each of which can be easily adapted for offensive efforts:


Furthermore, this Github member recommends methods to bypass patches:

Conclusion
Threat actors do not always need to search in the depths of the dark web to find high-value exploit codes. Very often, they can find exactly what they need on Github. Accordingly, to truly stay informed, prepared and protected from impending cyberattack, it is advised that defenders continue to monitor activity on Github. Doing so can provide insights about some of the tools that attackers have at their disposal. Additionally, examining the total amount of activity on Github can also produce critical intelligence insights, indicating the general levels of interest and threat of exploitation surrounding a particular vulnerability.
)
)
)
)